Multiple Choice
Identify the
choice that best completes the statement or answers the question.
|
|
|
1.
|
The most common transfer protocol used on the Internet is _____.
|
|
|
2.
|
The ____ is a self-organized group that makes technical contributions to the
engineering of the Internet and its technologies.
a. | Internet Engineering Task Force | b. | National Science Foundation | c. | Federal Networking
Council | d. | Global Addressing Consortium |
|
|
|
3.
|
The term ____ is used to describe LANs or WANs that use the TCP/IP protocol but
do not connect to sites outside the firm.
a. | telephone | b. | intranet | c. | Internet | d. | network
backbone |
|
|
|
4.
|
When you click on a ____, a new HTML document, such as a page of text and
graphics, or an audio or video file appears.
a. | user interface | b. | tag | c. | link | d. | hypermark |
|
|
|
5.
|
Which of the following sells access to the Internet to organizations and
businesses?
a. | Telnet | b. | Internet Service Providers
(ISPs) | c. | Internet Backbone | d. | Network access points
(NAPs) |
|
|
|
6.
|
____ tells Web browser software how to display text and other elements contained
in a document.
|
|
|
7.
|
The ____ domain name indicates a U.S. commercial enterprise.
|
|
|
8.
|
The ____ button allows you to return to the home page (or start page) for your
Web browser.
a. | back | b. | reload/refresh | c. | home | d. | stop |
|
|
|
Figure B-1
|
|
|
9.
|
In the Internet Explorer window shown in Figure B-1, the item marked 2 is the
____.
a. | title bar | b. | menu bar | c. | address
bar | d. | status bar |
|
|
|
10.
|
In the Internet Explorer window shown in Figure B-1, the item marked 3 is the
____.
a. | refresh button | b. | stop button | c. | home
button | d. | back button |
|
|
|
Figure B-2
|
|
|
11.
|
In the Firefox window shown in Figure B-2, the item marked 2 is the ____.
a. | Title bar | b. | Menu bar | c. | Location
bar | d. | Page tab |
|
|
|
12.
|
You can organize bookmarks and favorites by placing them in which of the
following?
a. | Folders | b. | A network | c. | The History
folder | d. | A file |
|
|
|
13.
|
Unsolicited e-mails usually selling an item or service are referred to as
____.
a. | Attachments. | b. | Webmail. | c. | Spam. | d. | Netiquette. |
|
|
|
14.
|
In Hotmail, messages that you delete are stored in the ______ folder until you
permanently delete them.
a. | Drafts. | b. | Inbox. | c. | Sent
Messages. | d. | Trash Can. |
|
|
|
Figure C-2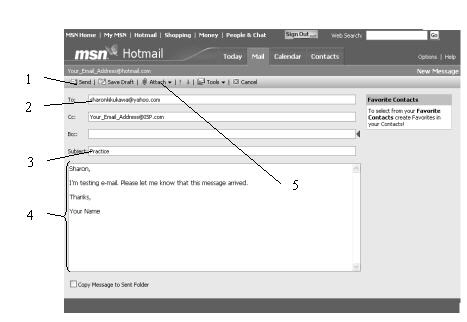
|
|
|
15.
|
In the Hotmail message window shown in Figure C-2, what is the function of the
item marked 1?
a. | Specify a file to send with the current message. | b. | Summarize the
content of the current message. | c. | Send the current message to its
recipients. | d. | Specify message recipients. |
|
|
|
Figure C-3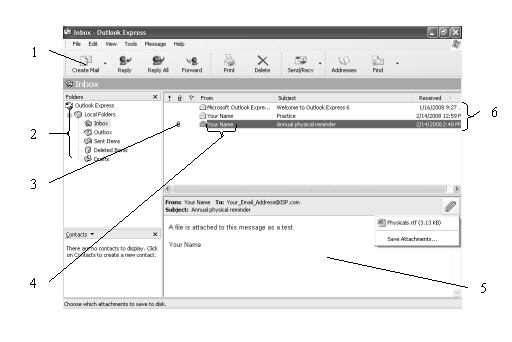
|
|
|
16.
|
In the Outlook Express Mail window shown in Figure C-3, which component is
marked as 2?
a. | Message summaries. | b. | Folders
list. | c. | Message pane. | d. | Message list. |
|
|
|
17.
|
You can use the ____ button to respond quickly and efficiently to the sender of
an earlier message.
a. | Reply. | b. | Reply All. | c. | Forward. | d. | All of the
above. |
|
|
|
18.
|
A group of keyboard characters that represent an emotion when viewed together is
called a(n) _____.
a. | Netiquette. | b. | Emoticon. | c. | E-mail
faces. | d. | Electronicon. |
|
|
|
19.
|
A Web robot deletes information in the search engine's ____ when a Web site
no longer exists.
a. | spider | b. | database | c. | spreadsheet | d. | archive |
|
|
|
20.
|
A Web ____ is a listing of links to Web pages that is organized into
hierarchical categories.
a. | directory | b. | database | c. | search
engine | d. | full-text indexed hierarchy |
|
|
|
21.
|
____ list Web pages selected by people rather than using a database compiled by
Web bots.
a. | Internet indexes | b. | Search engines | c. | Web
directories | d. | Meta-search engines |
|
|
|
22.
|
Which of the following uses human editors to select Web pages to be included in
the database organized into hierarchical categories?
a. | Search engine | b. | Web directory | c. | Meta-search
engine | d. | Web browser |
|
|
|
23.
|
Using a ____ lets you search several engines at the same time.
a. | search engine | b. | Web directory | c. | meta-search
engine | d. | Web bibliography |
|
|
|
24.
|
You can search for weather forecasts in cities around the world using an online
______ service.
a. | temperature | b. | city | c. | news | d. | weather |
|
|
|
Figure E-1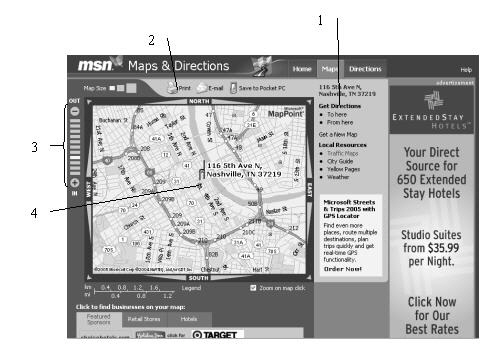
|
|
|
25.
|
Figure E-1, the item marked 1 does which of the following?
a. | Shows the location of the address you mapped. | b. | Prints the
map. | c. | Allows you to zoom in or out of the map. | d. | Displays driving
directions for the address you mapped. |
|
|
|
26.
|
A search engine that enables you to find businesses grouped by type and location
is called a _______.
a. | Web directory | b. | Yellow page directory | c. | White page
directory | d. | Map site |
|
|
|
27.
|
When you copy a work for use in criticism, comment, news reporting, teaching,
scholarship, or research, it is called _____.
a. | copyright | b. | citation | c. | fair
use | d. | plagiarism |
|
|
|
28.
|
A(n) ____ document contains answers to common questions that users ask about
mailing lists.
a. | FAQ | b. | help | c. | command | d. | archive |
|
|
|
Figure F-3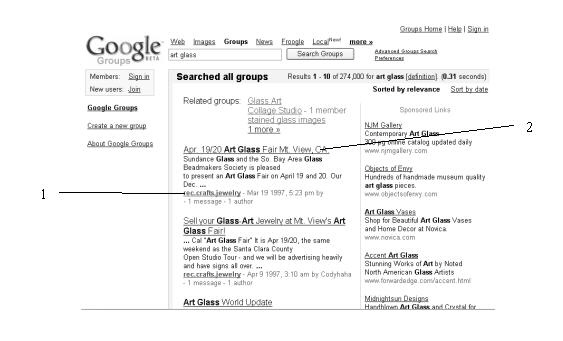
|
|
|
29.
|
Which communication tool is shown in Figure F-3?
a. | Chat | b. | A mailing list | c. | A
newsgroup | d. | None of the above |
|
|
|
30.
|
A(n) _______ chat occurs between individuals who are invited to participate in
the chat.
a. | public | b. | private | c. | open | d. | closed |
|
|
|
31.
|
To ____ a file means to receive the file on your computer from another
computer.
a. | download | b. | upload | c. | put | d. | retrieve |
|
|
|
32.
|
Which of the following is fully functional software that is available to anyone
at no cost and with no restrictions attached to its use?
a. | Limited edition software | b. | Freeware | c. | Shareware | d. | All of the
above |
|
|
|
33.
|
Which of the following resides on your computer and allows you to transfer files
between your computer and another computer connected to it using the rules for FTP?
a. | FTP server program | b. | HTTP server program | c. | FTP client
program | d. | Download program |
|
|
|
34.
|
Most images on the Web are in the ____ file formats.
a. | GIF and JPEG | b. | TIFF and PCX | c. | HTML and
SGML | d. | MPEG and WAV |
|
|
|
35.
|
Which of the following is not a file format used for audio on the Web?
a. | MP3 | b. | RealAudio | c. | AVI | d. | All of the above are used for
audio |
|
|
|
36.
|
Which of the following audio formats is the audio format used by the UNIX
operating system?
|
|
|
37.
|
Software that can only be started from within a Web browser and that displays or
plays specific file types is known as a(n) ____.
a. | streaming program | b. | clip art | c. | plug-in | d. | animated GIF |
|
|
|
38.
|
A browser extension that can start independent of a Web browser is known as a(n)
_____.
a. | helper application | b. | plug-in | c. | anti-virus
program | d. | worm |
|
|
|
39.
|
Which type of browser extensions let you use a Web browser to read documents,
such as those in PDF format?
a. | Animation | b. | Document and productivity | c. | Image
viewer | d. | Sound player |
|
|
|
40.
|
Which type of browser extensions allow you to play interactive games and view
Shockwave and Flash files?
a. | Animation | b. | Document and productivity | c. | Video
player | d. | Sound player |
|
|
|
41.
|
A tool known as a ____ can capture data being transmitted on a network,
including user names, passwords, and other personal information.
a. | packet sniffer | b. | JavaScript program | c. | cookie | d. | virus |
|
|
|
42.
|
When an individual tries to obtain confidential information from people via
e-mail by pretending to be a familiar organization or institution, it is called _____.
a. | phishing | b. | phinding | c. | phoning | d. | pharming |
|
|
|
43.
|
A ____ on a computer permits traffic to enter and leave a computer.
a. | port | b. | pane | c. | post | d. | peephole |
|
|
|
44.
|
Which of the following is the word used to describe a Web site that looks like
it belongs to one organization but actually belongs to someone else?
a. | Spinned | b. | Spammed | c. | Spoofed | d. | Shared |
|
|
|
45.
|
Someone could use open _______ on your computer to access data on your
computer.
a. | doors | b. | windows | c. | ports | d. | panes |
|
|
|
46.
|
Which of the following describes the process of scrambling and encoding data
transmissions using a mathematically-based program?
a. | Encryption | b. | Enclosed | c. | Stealth | d. | Hidden |
|
|
|
47.
|
Informed Web users can implement ____, which are procedures, programs, and
hardware that detect and prevent computer security threats.
a. | viruses | b. | applets | c. | cookies | d. | countermeasures |
|
|
|
48.
|
Some Web sites store information on your computer in small text files known as
____.
a. | applets | b. | cookies | c. | viruses | d. | worms |
|
|
|
49.
|
A general category of software that includes advertisements to help pay for the
product in which they appear is ___________.
a. | Web bugs | b. | cookies | c. | adware | d. | spyware |
|
|
|
50.
|
You can keep viruses, worms, and Trojan Horses from using your e-mail program to
reproduce by installing ____.
a. | applets | b. | anti-virus software | c. | pretty Good Privacy
(PGP) | d. | browser extensions |
|